The working principle of the camera can be divided into four key steps: optical imaging, electrical signal conversion, digital signal processing and image output.
Encyclopedia
The principle of wireless charging is through near-field induction, the wireless charging device conducts energy to the charging terminal device, and then the terminal device converts the received energy into electrical energy and stores it in the device's battery.
3D stereo glasses is a penetrating LCD lens, through the circuit to the LCD glasses on, off the control, on can control the glasses lens all black, in order to cover a glance image; off can control the glasses lens for transparent, so that the other glance to see another glance should see the image.
With the development of holographic projection technology, the introduction of multimedia interactive technology in the construction of corporate exhibition halls, focusing on intelligent multimedia interaction, immersive participation experience, and the visual sense of science and technology, the digital exhibition hall brings a novel sense of participation and interaction to people.
SLR digital cameras and we are more in contact with the ordinary consumer digital cameras are two completely different systems, the difference here is mainly reflected in the internal structure of the two.
If the user wants to extend the effective service life of the battery, in addition to the quality of the charger, the correct charging method is also essential, because the poor quality charger or the wrong charging method will affect the service life and cycle life of the battery. Here are the tips on extending the life of the mobile phone charging battery that the author has compiled:
SSDs have been sold for a long time. However, at present, mainstream installations are still purchasing traditional mechanical hard disks, while most SSDs are installed in high-end configurations. Due to the small capacity and high price of SSDs at present, few mainstream users choose SSDs. However, with the development of technology, it is also a trend that SSDs gradually become mainstream. Next, we will introduce the advantages of SSDs and the differences between SSDs and ordinary HDDs.
Switch, meaning "switch", is a network device used for electrical (optical) signal forwarding.
The working principle of the projector is based on the fusion of optical and electronic technologies.
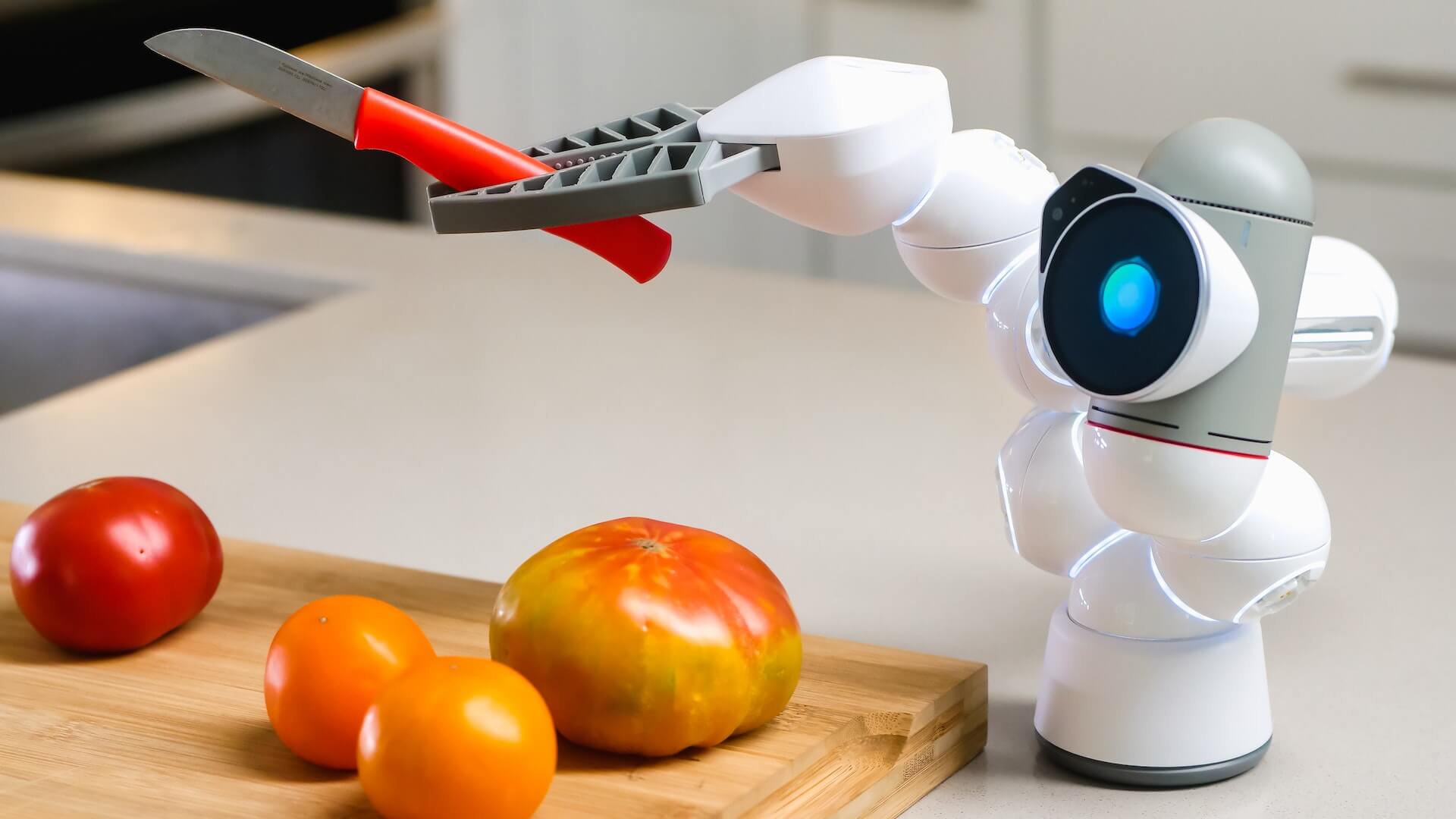
Machine vision technology aims to simulate and emulate the human visual system through algorithms and models that enable computers to "see" and understand information in images or videos.