iCloud as a cloud service provided by Apple, users can get 5GB of cloud space for free, if more than 5GB of space we need to buy space, then there is no other way to solve it?
Encyclopedia
Router in the process of use, will produce a lot of junk files, we need to regularly clean up these cache, so as to improve the network speed, if not shut down for a long time as more and more of this junk, the operating speed will be reduced.
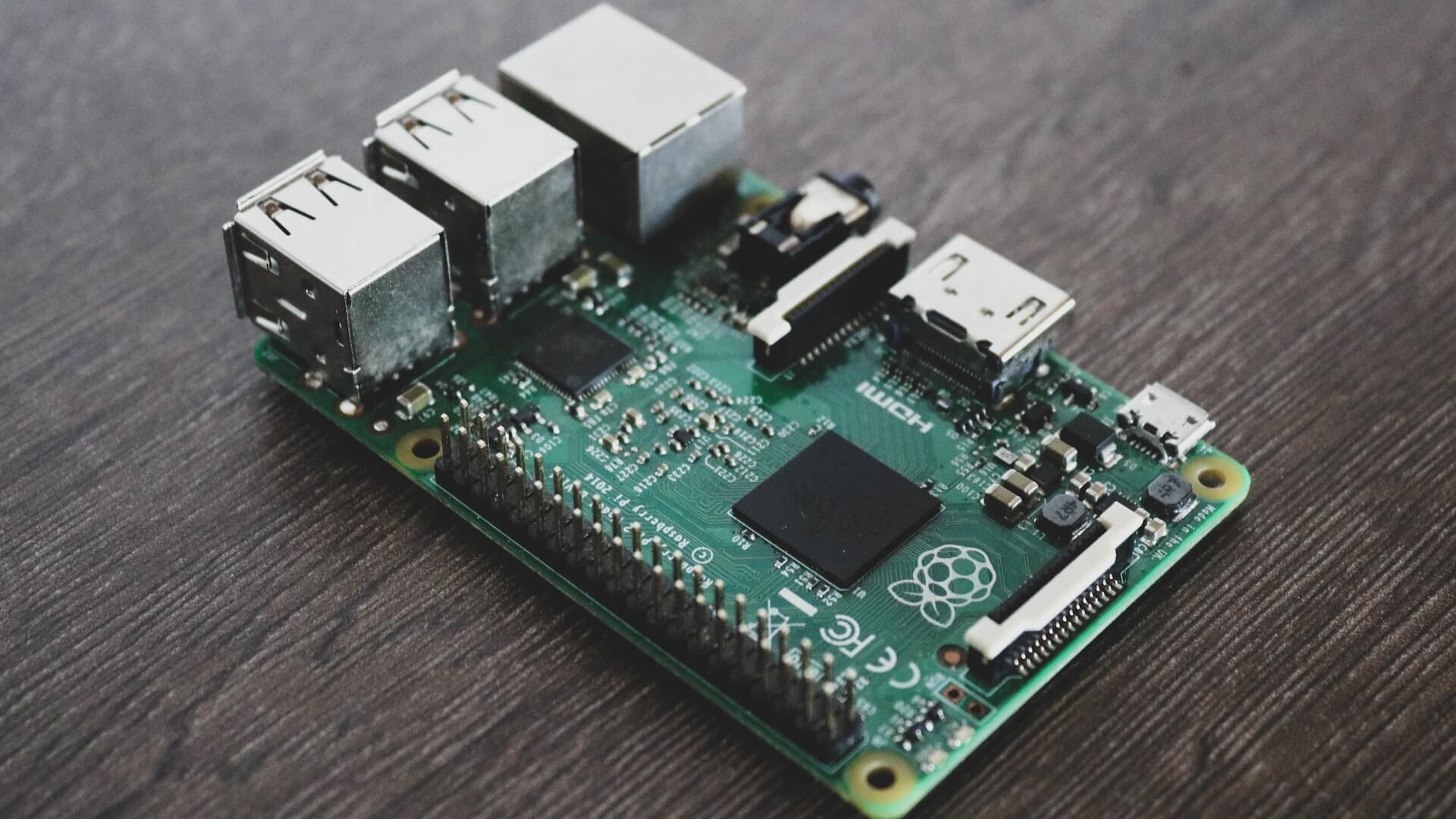
A chip is a tiny circuit board made of semiconductor materials such as silicon on which a large number of electronic components, such as transistors, capacitors, resistors, etc., are integrated.
The working principle of power adapter and charger is the same, both use the principle of AC power conversion to convert AC power into DC power to meet the power needs of the device.
IMEI code, namely the serial number of the mobile phone. It is the abbreviation of International Mobile Equipment Identity. Like the identity card of a mobile phone, it is used to help identify the identity of a mobile phone. Each mobile phone has only one serial number, which is not the same. We usually match the serial number displayed after pressing the "* # 06 #" key on the mobile phone with the barcode on the mobile phone box and the serial number in the back of the mobile phone after removing the electric board. If the three are the same, it is more likely to be genuine goods (not excluding second-hand goods).
Discrete graphics card refers to a graphics card that exists as an independent board and needs to be inserted into the corresponding interface on the motherboard. Discrete graphics card has independent video memory, does not occupy system memory, and is technically ahead of integrated graphics card, which can provide better display effect and operating performance. Discrete graphics cards are divided into built-in discrete graphics cards and external graphics cards. As an important part of the computer host, the graphics card is very important for those who like to play games and engage in professional graphic design. At present, the suppliers of graphics chips for civilian graphics cards mainly include AMD (formerly ATI) and nVIDIA.
As an advanced means of identity verification and access control, fingerprint recognition technology has been widely used in various fields with the advantages of uniqueness, convenience and high security.
What is the reason for the computer card? How to deal with the computer card? Here are the main reasons why computers are getting more and more stuck
Cell phone battery is an important part of the phone, and its life and capacity directly affect the experience of using the phone. So, how should we charge the phone properly?
The mouse and keyboard, like, is to assist us in computer operation equipment, but compared to the desktop mouse, the laptop mouse seems to be more problems